geofencing
What is geofencing?
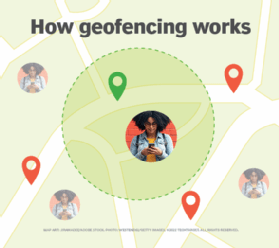
Geofencing is a type of location-based marketing and advertising. A mobile app or software uses the Global Positioning System (GPS), radio frequency identification (RFID), Wi-Fi or cellular data to define a virtual geographical boundary and trigger a targeted marketing action when a device enters or exits that boundary. This boundary is known as a geofence.
Geofencing, sometimes spelled geo-fencing, can also allow a user to set up triggers so that when a device such as an internet-connected smartphone enters a defined geographical boundary, the user gets an alert. They can also initiate some specific action targeting that device.
An example of geofencing used in marketing is when a student and a working professional walk near a computer store, and then both receive a text message that says, "Today only! Buy a laptop and get an e-reader free!"
The users get the text because they are near a store that has a geofence that automatically triggers a targeted marketing action -- the text message. The store could also geotarget users with in-app notifications, social media ads, push notifications, emails, etc.
The virtual boundaries or geofences can be active or passive. Active geofences require an end user to opt in to location services and a mobile app to be open. Passive geofences are always on; they rely on Wi-Fi and cellular data, and work in the background.
How does geofencing work?
Geofencing requires communication technologies such as GPS, RFID, Wi-Fi or cellular data. Once a marketer sets up a geofence, a preprogrammed action is automatically triggered when a mobile device or RFID tag enters or exits the geofence. A virtual boundary can be created around a geographical location as small as a building, store or mall, and as large as a ZIP code, city or entire state.
An administrator or developer first establishes a virtual boundary around a certain location in GPS- or RFID-enabled software. They can use polygonal geofencing software to identify points on a map. These points define the boundary where they want to capture people or devices.
More commonly, geofences are defined by drawing a circle around the desired location on Google Maps using the application programming interfaces, or APIs, created during app development. The circle represents the geofence that will trigger a response whenever an authorized device enters or exits that area. The response is preprogrammed by the admin or developer.
Many geofencing applications incorporate Google Earth, allowing administrators to define boundaries on top of a satellite view of a specific geographical area. Other applications define boundaries by longitude and latitude or through user-created and web-based maps.
What is user-defined geofencing?
While businesses and marketers commonly use geofencing, individual users can also set up geofencing in their mobile apps. These apps allow them to select an address or location where they want to trigger a specific alert or push notification.
In this case, geofencing uses an "if this, then that" command that allows the app to trigger an action based on another action. For example, the user can program a command in the app such as, "If I lock the front door, turn on the porch light." Similarly, they can use a reminder app to send an alert when they reach a certain location. For example, "When I approach the office building, remind me to wear my ID card."
What are some benefits of geofencing?
Geofencing enables marketers to target prospects with engaging messages and attractive offers. It can improve customer engagement because geofencing can target a specific demographic within a defined geographical area that's further filtered using targeted criteria. This type of targeted advertising improves engagement numbers and ad spend effectiveness.
Businesses can also use geofencing to draw prospects away from the competition and boost their own traffic and sales. And geofencing provides insightful data that helps marketers improve their campaigns. This includes data about foot traffic, stay durations, conversions, etc. Marketers can combine this data with information about users' online activities, purchase habits and web browsing behaviors to personalize campaigns and improve user experiences.
Another advantage of geofencing is that it allows businesses to create omnichannel marketing campaigns to further boost sales and revenues.
In addition to marketing, geofencing has other applications because it is mobile-centric. Any company can deploy geofencing on a range of mobile devices, including smartphones, tablets and smartwatches, for marketing, advertising, tracking, security management, law enforcement and more.
What are some applications of geofencing?
Geofencing is commonly used as a marketing and advertising tactic to pull in more customers to a brick-and-mortar business, such as a store. For example, a business can send in-app notifications on its own app when a user who has that app on their device enters a geofenced area.
Businesses also use geofencing to target users on other apps. One example is a restaurant, movie theater or salon sending coupons over a coupon app once a consumer enters a geofenced area. Some businesses leverage the geofencing capabilities of social media apps such as Facebook or Instagram to send ads to consumers who enter a geofenced area. They can also use search engines such as Google to send targeted ads to users who cross into a predefined geographical area.
Some marketers use geofencing to attract users who are visiting a competitor's business. In this scenario, business X sets up a geofence around business Y so that when a consumer enters the boundary, they receive a push notification or Short Message Service text message prompting them to leave business Y and visit business X.
In addition to marketing and advertising, geofencing is also used for these real-world applications:
| Use | Example |
| Drone management during events | A sporting event can use geofencing to create a temporary no-fly zone that prevents drones from crossing a defined perimeter. |
| Drone management for security | Airports, government buildings, military camps and other sensitive areas can set up drone-resistant geofences that will stop a drone in midair, trigger a warning message to the user or ask for the user's authorization to operate the drone in that area. |
| Audience engagement at events | Event organizers can use geofencing to engage with the audience before or during the event. |
| Shipping and fleet management | Geofencing can alert a dispatcher when a truck driver deviates from their route. |
| Human resource security management | An employee's smart card can send an alert to security if the employee attempts to enter an unauthorized geofenced area. |
| Human resource time management | Company managers can use geofencing-enabled software to track employees' time and resource use. |
| Compliance management | Network logs can record geofence crossings to document the proper use of devices and confirm compliance with established policies. |
| Asset management | A company network administrator can set up alerts when a company-owned device leaves the premises so that they can find its location and lock it down to prevent misuse by unauthorized users, e.g., thieves. |
| Law enforcement | An ankle bracelet can alert authorities if an individual under house arrest has left the premises without prior authorization. |
| Home automation or smart homes | When a homeowner's smartphone enters the home's geofenced perimeter, the thermostat can adjust itself to a predefined temperature or the lights can automatically turn on. |
| Animal tracking | Pet owners and farmers can set up geofences to alert them when an animal leaves the boundary, allowing them to track the animal. |
See how effective geofencing technology is as a security method.
